📅 What happened after Vegas
Last time I wrote, I was packing for BlackHat and DEFCON and pretending that travel chaos is a lifestyle choice. Since then there have been flights, workshops, a Japan detour, more browser tools, and now a London and Bangalore run lined up.
If you want to catch me live, this is a good window.
🏴 Coming up in London: Black Hat Europe 2025
0wning the Cloud: AWS, Azure, GCP, DigitalOcean and Aliyun Two day, deep dive, multi cloud hacking training at Black Hat Europe 2025. We work through real world misconfigurations, pivot paths, and abuse patterns across the big providers, with scenario driven labs and a very attack first mindset.
- Dates: 8 to 9 December 2025
- Location: ICC Maritime Suite, Trinity 1 and 2, Level 3
- More details and registration
If you work anywhere near cloud infra or security and want two days of focused, hands on pain in a controlled environment, this one is for you.
Birds of a Feather: A Candid Conversation on Software Supply Chain Security
I will be moderating a community conversation on software supply chain security with, Rami McCarthy (Wiz), Pamela O’Shea, Ph.D. (Shea Security), Himanshu Kumar Das (Cred). We will talk frankly about what is working, what is theater, and how to move beyond buzzwords into actual risk reduction in the supply chain.
- Date: Thursday, 11 December 2025
- Time: 1:30 pm to 2:10 pm
- Location: ICC Maritime Suite, Victoria 2, Level 3
Bring questions, war stories, and strong opinions.
Arsenal: SBOMPlay live at Black Hat EU
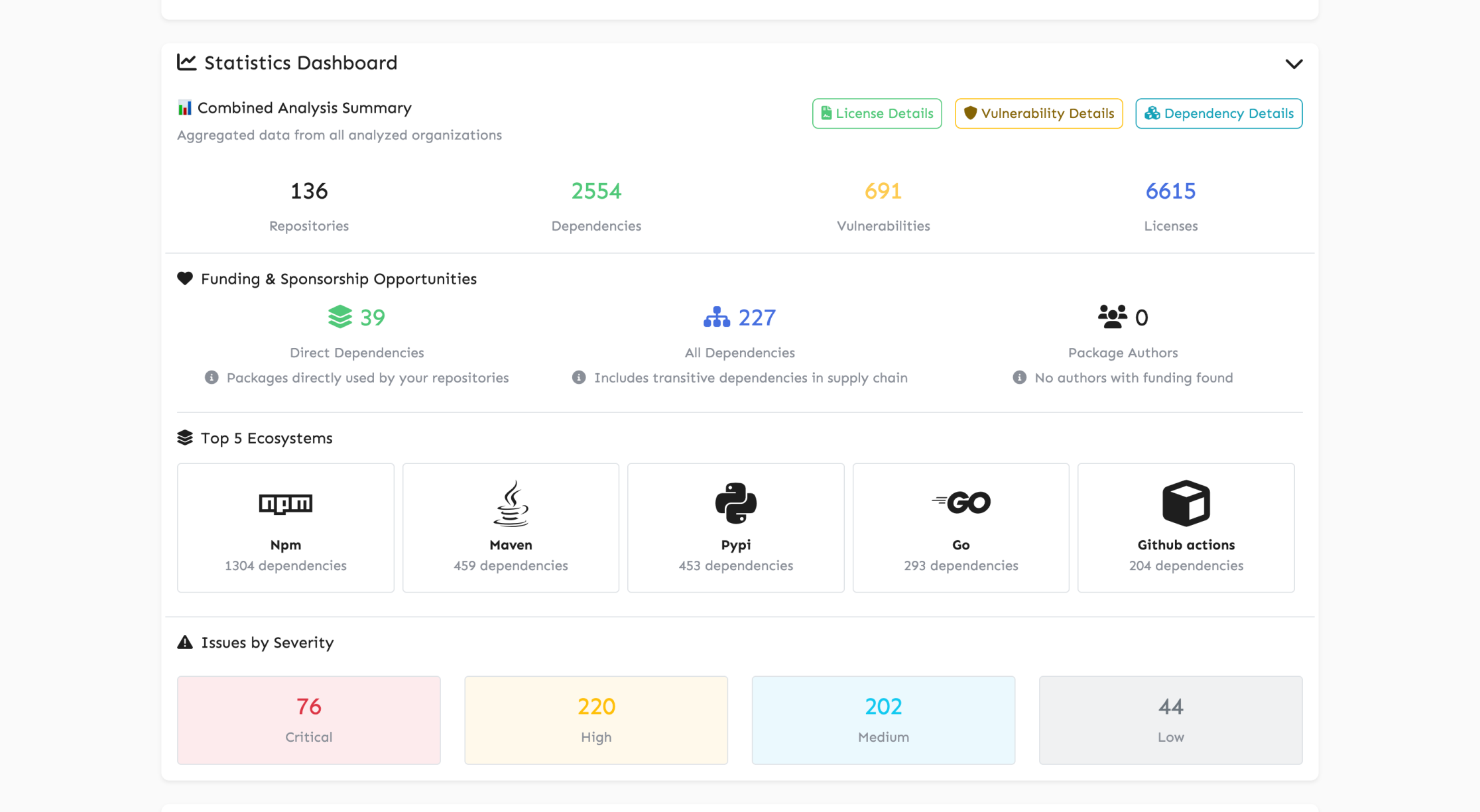
I will also be in the Arsenal area to walk through SBOMPlay in person. SBOMPlay is my browser only SBOM explorer for doing fast multi SBOM analysis, mapping dependency and license sprawl, and generally making sense of the mess we call software supply chain.
- Date: Wednesday, 10 December 2025
- Time: 2:30 pm to 3:50 pm
- Location: Arsenal Station 4, Business Hall
If you want to see how far you can push SBOMs without shipping any data to a backend, come hang out. Check these pics to get a sneak peak and feel free to try it out here
🛰 Next stop Bangalore: Byt3con HACK THE CLOUD
If London is too far, or you want a quieter setting than a Black Hat hallway, I will be in Bangalore with Byt3con.
HACK THE CLOUD: Exploiting AWS and Google Cloud for Fun and Profit
Three day, lab heavy training focused on finding and exploiting misconfigurations in AWS and Google Cloud. We start from setting up your own cloud environments, move into discovery and chaining of issues, and end with attacker style objectives in mind.
- Dates: 22 to 24 January 2026
- Time: 9:00 am to 5:30 pm (GMT+05:30)
- Venue: Royal Orchid - Bangalore
If you are in India and want a focused cloud hacking immersion without international travel, this is your best bet for early 2026.
🎙 Talking instead of just typing
A Day in the Life of an Entrepreneur Podcast Vandana Verma invited me to her series to talk about the not so glamorous side of being an entrepreneur and community person. We spoke about juggling trainings, Cyfinoid, and community work without burning everything down at once.
Breakpoint Security Podcast with Neelu Tripathy Another long form conversation, this time with Neelu, around career paths, security, and how this space keeps evolving while we try to stay sane inside it.
🇯🇵 From Tokyo, with fewer attack surfaces
In October I finally made it to Japan for Security Days Fall; I did a set of workshops & a talk.
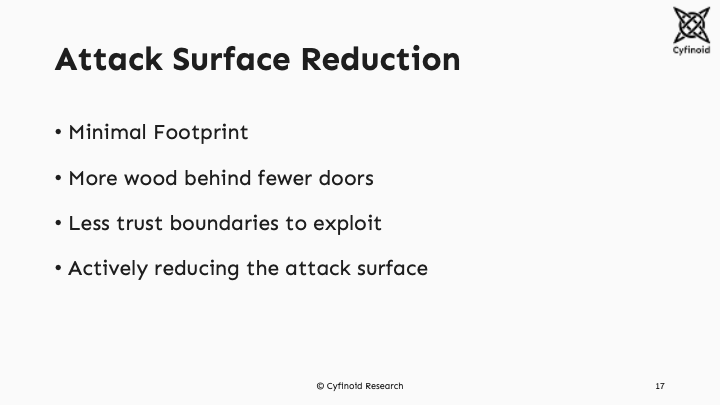
From AI to the supply chain: Why reducing the attack surface is no longer an option This talk connected AI assisted development, messy software supply chains, and overgrown infrastructure into one problem: attack surface explosion. The core idea was simple. We cannot keep adding more tools on top and hope it works. We have to reduce what we expose in the first place. 🔗 Slides here
With Benefits for management
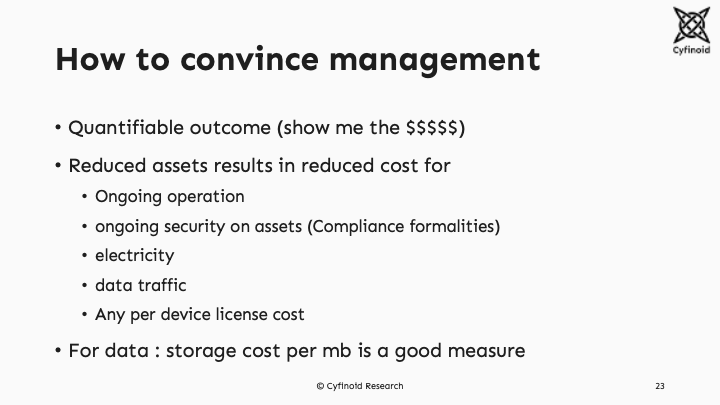
I truely belive that the way forward is to holistically aim towards reducing the attack surface. https://reducetheattacksurface.com/ is the manifesto i have made public and i will be working in next few months to refine and add more content.
🧩 New tool and updates on existing tools
Most of my free time still goes into taking the browser first, privacy first idea and pushing it further. Cyfinoid Research we are trying to make tools as simple to use as possible.
SBOMPlay SBOM explorer in the browser. Point it at SBOMs from your repos and it helps you understand dependency, license, and version sprawl without sending data outside your machine. 🔗 App: https://cyfinoid.github.io/sbomplay/ 🔗 Code: https://github.com/cyfinoid/sbomplay
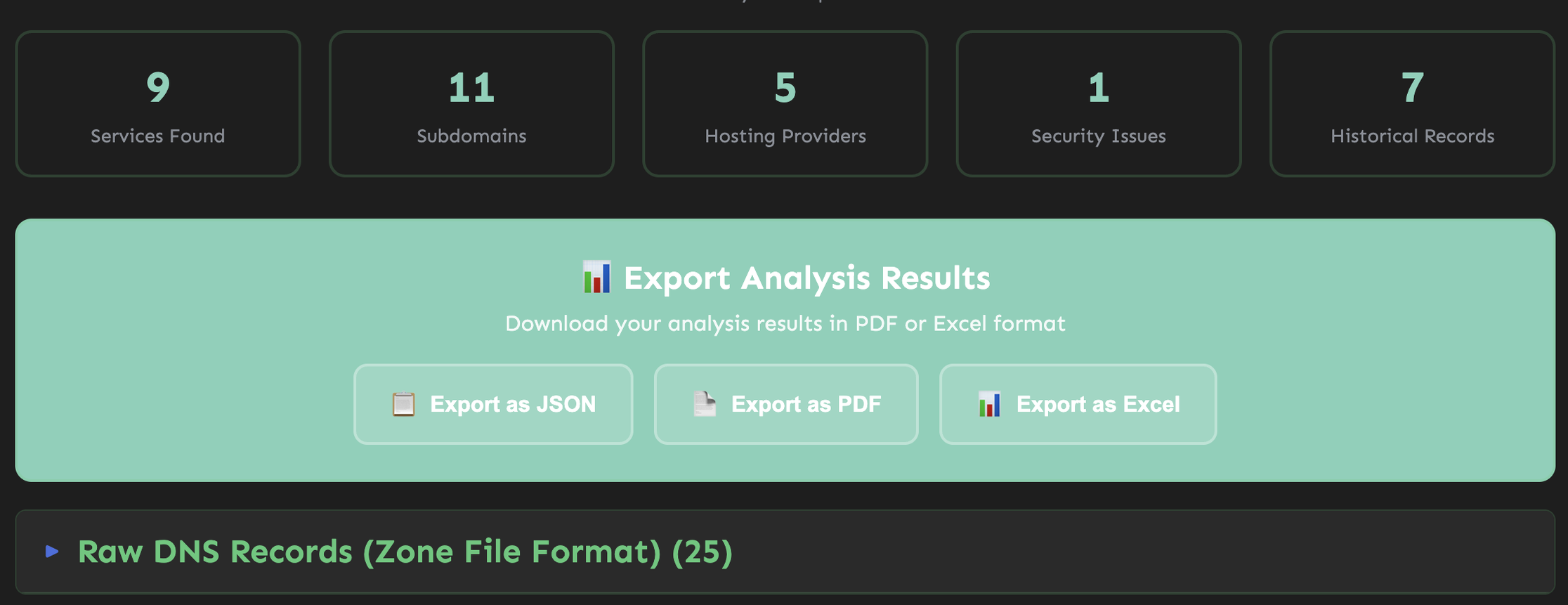
3PTracer DNS driven recon for mapping third party services that touch your domain and traffic. Handy for data flow mapping and vendor risk questions. 🔗 App: https://cyfinoid.github.io/3ptracer 🔗 Code: https://github.com/cyfinoid/3ptracer
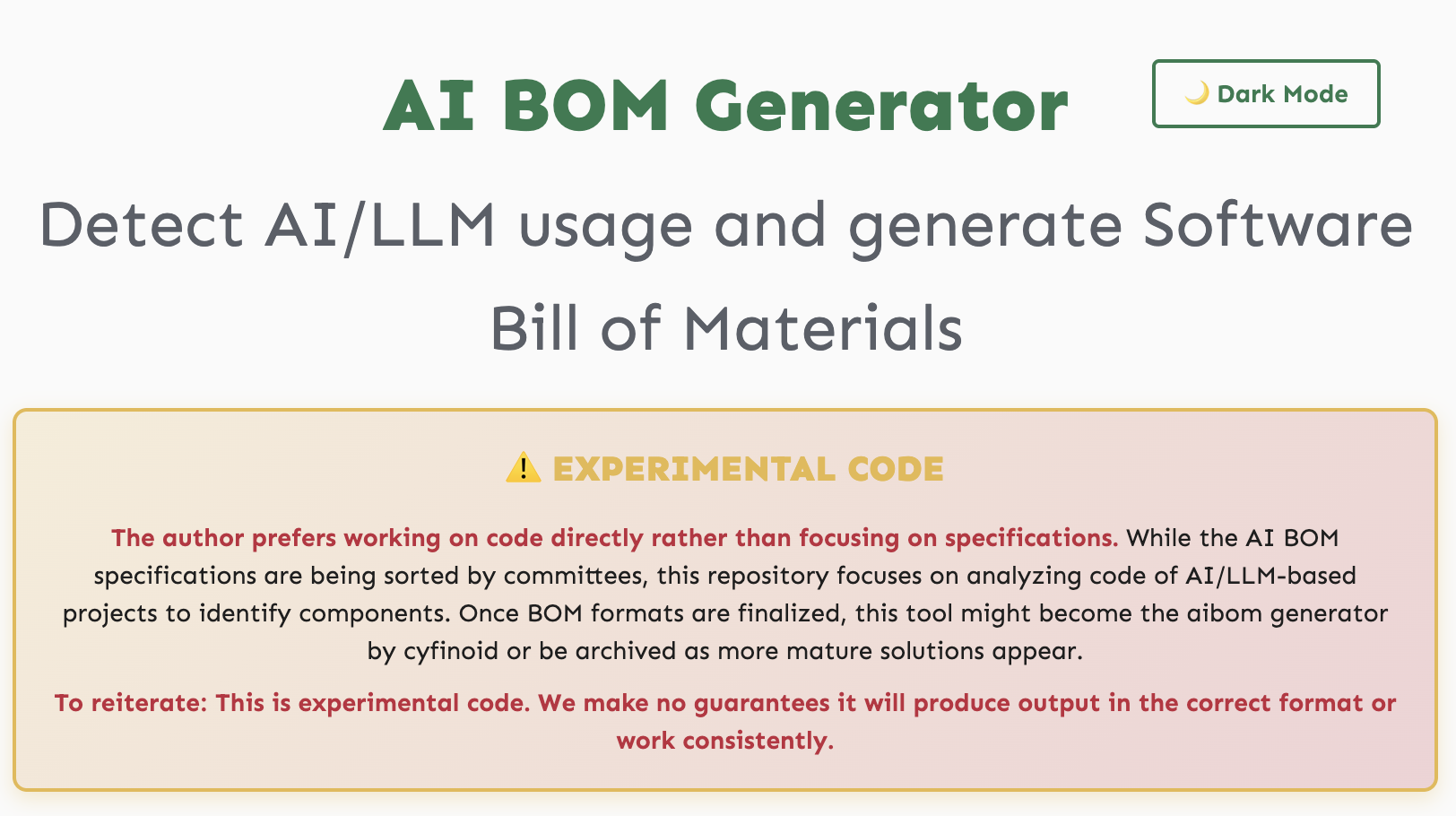
AIBOMMaker Experimental AI Bill of Materials generator. It scans GitHub repos for signs of LLM or AI usage in code, configs, CI and then lets you export an AI focused BOM in standard formats. 🔗 App: https://cyfinoid.github.io/aibommaker/ 🔗 Code: https://github.com/cyfinoid/aibommaker
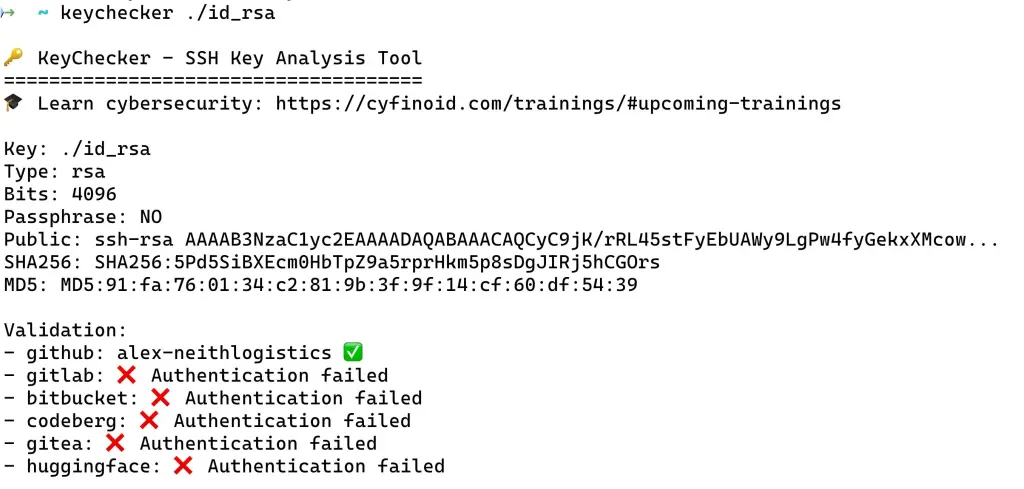
KeyChecker CLI that takes an SSH key and asks which Git hosting accounts that key can talk to. Very useful for both defenders checking key hygiene and attackers mapping potential blast radius. 🔗 Code: https://github.com/cyfinoid/keychecker 🔗 PyPI: https://pypi.org/project/keychecker
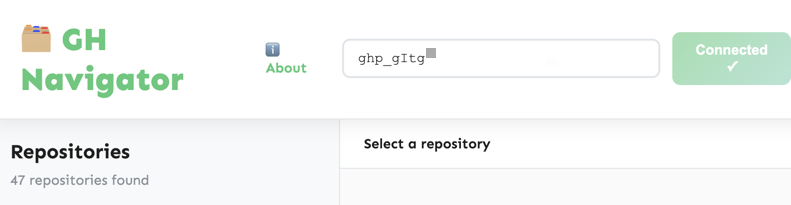
GH Navigator Browser only GitHub navigator and token analyser. Explore orgs and repos without cloning everything, and understand what your tokens can really do. 🔗 App: https://cyfinoid.github.io/ghnavigator 🔗 Code: https://github.com/cyfinoid/ghnavigator
Cloud IAM Policy Explorer AWS IAM policy explorer that helps you spot shadow admins and privilege escalation paths by turning JSON walls into something more readable. 🔗 App: https://cyfinoid.github.io/cloud-iam-policy-explorer/ 🔗 Code: https://github.com/cyfinoid/cloud-iam-policy-explorer

Hugo Techie Personal theme The Hugo theme that powers my own site is now public. It is tuned for people who want a living timeline of talks, tools, and projects instead of a static CV. 🔗 Theme: https://github.com/anantshri/hugo-techie-personal Live demo is available on my own website : https://anantshri.info
✍ Writing, because code is not enough
Not Every Nail Needs a Non Deterministic Hammer On where non deterministic systems like LLMs actually help, and where they just add noise to systems that need reliability. 🔗 https://blog.anantshri.info/not-every-nail-needs-a-non-deterministic-hammer
Hacker vs Adversary On why “hacker” is a mindset and “adversary” is a role, and how mixing the two confuses our security stories. 🔗 https://blog.anantshri.info/hacker-vs-adversary
What LLMs Teach Me About My Own Brain On using LLMs as a mirror to examine attention, context, and how we outsource thinking. 🔗 https://blog.anantshri.info/what-llms-teach-me-about-my-own-brain
Making Security Tools Accessible: Why I Chose the Browser On the design rules behind most of the tools above. Client side first, no surprise data collection, and focusing on accessibility for practitioners. 🔗 https://blog.anantshri.info/making-security-tools-accessible-why-i-chose-the-browser
🧩 How you can plug into all this
- If you are headed to London, join the 0wning the Cloud training, the supply chain BoF, or the SBOMPlay Arsenal session.
- If you are in or near Bangalore, consider the HACK THE CLOUD training at Byt3con in January.
- If travel is not on the cards, run your own SBOM, DNS, AI and IAM experiments with the browser tools and tell me what breaks.
And as always, if you feel someone is missing from Hacking Archives of India, or something should be preserved before it disappears, you know where to find me.
Until the next round of tools, talks and travel chaos, keep hacking.